What is VPN and How Does It Work? The 2026 Guide for India’s Remote Workforce
A Virtual Private Network (VPN) encrypts your internet connection to protect data from hackers on public Wi-Fi networks. With India experiencing a massive surge to over 403 million active users, VPNs provide the mandatory secure tunnel needed for remote corporate access.
The Engineering Behind Secure Remote Access
A VPN works by routing your device’s connection through a private server rather than your local ISP. This process masks your IP address and wraps your data in unbreakable encryption.
The Core Mechanics of IPsec Tunneling
To truly grasp what is VPN technology, you must understand the underlying tunneling protocols. When you connect your laptop from a busy cafe in Bengaluru, your raw data is highly vulnerable. A VPN creates a secure, heavily encrypted tunnel between your remote device and the central corporate network. This virtual barrier prevents “Man-in-the-Middle” attacks from intercepting sensitive company files. The enterprise industry standard relies heavily on Internet Protocol Security (IPsec). According to Cisco’s technical documentation, IPsec authenticates and encrypts every single data packet transmitted. This complex mathematical process ensures that even if packets are intercepted, the data remains entirely unreadable. The protocol establishes a secure handshake before any information is ever exchanged. This guarantees that both the sender and the receiver are fully verified and authenticated.
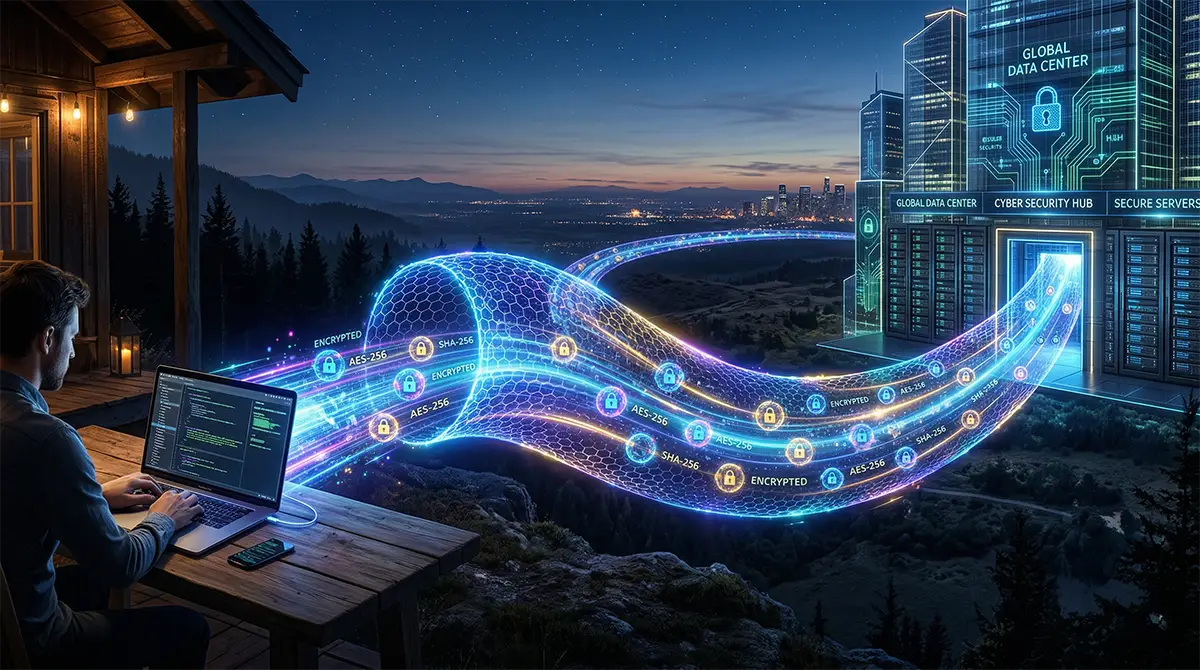
Why Remote Access Requires Advanced Cryptography
The sheer volume of Indian remote work demands exceptionally robust cryptographic standards to prevent corporate espionage. Advanced Encryption Standard (AES) utilizing 256-bit keys is the absolute baseline benchmark today. This military-grade encryption scrambles your data thoroughly before it ever leaves your local device. It only decrypts upon reaching the designated, secure corporate server. Fortinet’s 2026 glossary highlights that remote access VPNs are structurally essential for modern distributed workforces. They enforce zero-trust security principles seamlessly across hundreds of endpoints. Remote employees can securely access internal cloud applications without exposing the broader internal network to external threats. Cryptography ensures that your VPN meaning extends far beyond simple privacy into absolute data integrity. Without this encryption, digital commuters risk exposing proprietary code, financial records, and client databases.
Optimizing Speed with Split Tunneling Architecture
A common professional concern revolves around how VPN works regarding live connection speeds. Heavy encryption naturally adds a slight processing overhead, which can potentially cause unwanted latency. To actively counter this issue, enterprise VPN solutions employ a feature called split tunneling. This architectural feature allows you to route highly sensitive corporate traffic directly through the encrypted VPN. Meanwhile, routine, low-risk internet traffic, like streaming background music, uses your regular local ISP connection. This drastically reduces bandwidth consumption and processing load on the central corporate server. Indian remote workers can maintain high-speed access to heavy cloud applications without compromising strict security protocols. Split tunneling provides the perfect balance between zero-latency performance and absolute cryptographic safety for daily operations. It effectively solves the historic problem of network bottlenecking during peak regional business hours.
The Financial ROI of Enterprise-Grade Security
Investing in a corporate VPN yields a massive return on investment by actively preventing costly data breaches. The average cost of cyber incidents far outweighs the minor monthly subscription of secure access.
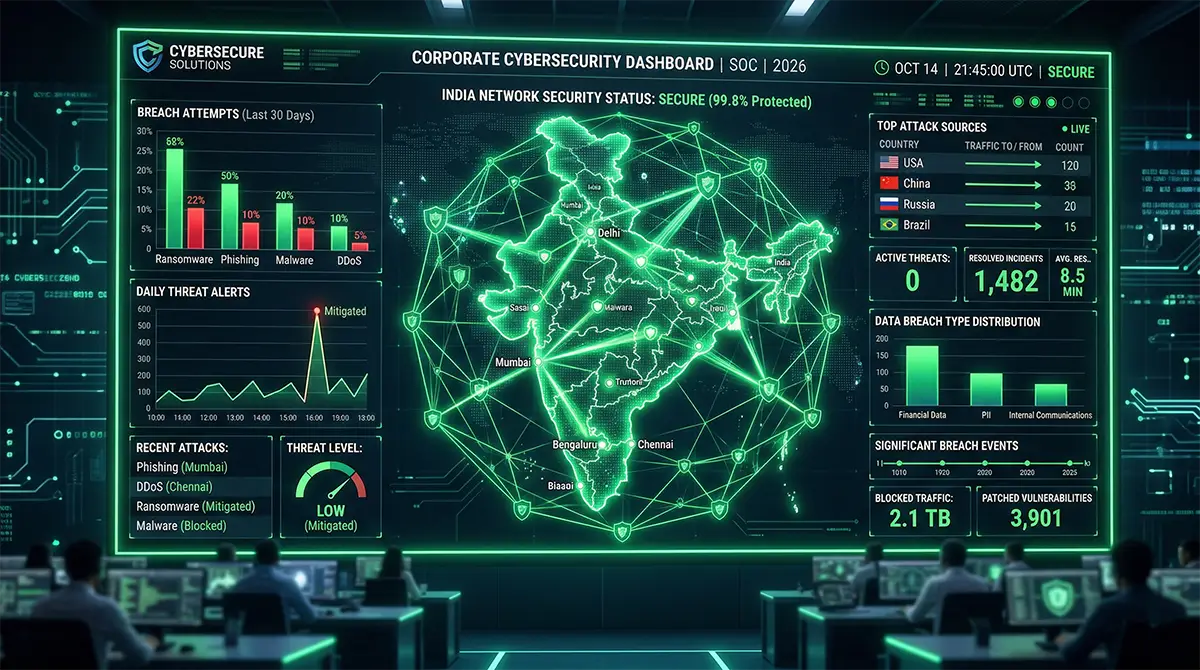
The Hidden Costs of Unsecured Public Wi-Fi
Working remotely from public spaces introduces severe, often uncalculated financial risks to modern Indian organizations. Unsecured cafe and airport networks are prime, easy targets for packet sniffing and unauthorized access. A single compromised remote device can easily lead to a catastrophic corporate data breach. The financial fallout includes heavy regulatory fines, lost intellectual property, and severe, lasting reputational damage. A recent Accenture State of Cybersecurity Resilience Report paints a rather grim picture of this landscape. It indicates that an alarming 92% of Indian firms remain woefully unprepared for modern security risks. These companies essentially operate directly within the highly dangerous “Exposed Zone.” Deploying a robust VPN mitigates this massive financial liability almost instantly upon activation. Ignoring this risk drastically increases the Maximum Cost Penalty (MCP) an enterprise faces during an audit.
Calculating the True Value of Digital Protection
The economics of enterprise VPN deployment are highly favorable for modern companies focused on scaling safely. A corporate-grade VPN typically costs only a few hundred rupees per remote user monthly. Compare this minor operational expense to the millions lost during an average data breach in India. The Return on Investment (ROI) becomes immediately apparent to any financial officer reviewing the IT budget. Beyond simple breach prevention, VPNs actively boost daily productivity by ensuring highly reliable network uptime. Remote employees face significantly fewer connection drops and completely avoid ISP throttling during critical client tasks. This uninterrupted operational continuity translates directly into sustained, predictable revenue generation for the business. A secure digital commuter is an efficient, highly profitable asset to the overall corporate structure. Let us clearly break down the comparative economics of remote security infrastructure.
| Security Metric | Without Corporate VPN | With Corporate VPN |
|---|---|---|
| **Data Breach Risk** | Critical (High probability on public Wi-Fi) | Minimal (Encrypted tunnels block interception) |
| **Regulatory Fines** | High (Non-compliance with data protection laws) | Zero (Meets strict encryption mandates) |
| **Productivity Loss** | Frequent (ISP throttling and blocked sites) | Rare (Optimized routing and split tunneling) |
| **Estimated Annual Cost** | ₹50,00,000+ (Average incident recovery) | ₹8,000 - ₹15,000 (Per user subscription) |
Benchmarking Top Tier Solutions for Digital Commuters
Choosing the right VPN requires balancing strict security protocols with low-latency performance. Leading solutions offer dedicated IP addresses and localized Indian virtual servers for optimal remote work.
The Surge of Virtual Privacy in India
India has recently witnessed a massive, unprecedented explosion in virtual privacy tool adoption across all sectors. Recent verified data from a Nym Security Analysis documents this remarkable, ongoing national trend clearly. The detailed report highlights an incredible surge to over 403 million active Indian VPN users. This massive growth is driven heavily by increasingly stringent remote data protection requirements and privacy laws. Digital professionals demand highly reliable platforms that will not compromise their fast-paced daily workflow. A lagging connection can ruin a crucial client presentation or delay urgent code deployments. Therefore, evaluating the underlying architecture of available commercial platforms is absolutely critical for IT decision-makers. Let us compare two leading corporate solutions perfectly tailored for this demanding Indian environment.
Solution Alpha: NordLayer for Enterprise Security
NordLayer is designed specifically for scalable corporate security and agile remote engineering teams. It smoothly transitions traditional, clunky VPN architecture into a modern Secure Access Service Edge (SASE). This platform excels in providing strict zero-trust network access to Indian professionals working globally. It offers highly stable dedicated gateways, ensuring remote workers consistently experience high-speed, secure connections. The central administration panel is highly intuitive for IT managers actively tracking remote user access. NordLayer strategically employs AES-256 encryption alongside the incredibly rapid, lightweight WireGuard protocol. This powerful combination ensures the VPN meaning translates to both impenetrable security and high performance. It features a robust kill switch that severs internet access if the secure connection drops.
| Technical Details | NordLayer Specification |
|---|---|
| **Encryption Standard** | AES-256 integrated with WireGuard Protocol |
| **Indian Server Presence** | Virtual localized servers via Singapore/UK routes |
| **Primary Structural Benefit** | Highly scalable zero-trust access control |
| **Ideal Corporate Fit** | Medium to large distributed enterprise teams |
Solution Beta: Perimeter 81 Cloud Architecture
Perimeter 81 takes a highly robust, completely cloud-native approach to modern distributed network security. It fundamentally eliminates the tedious need for legacy, highly expensive hardware-based VPN infrastructure entirely. Indian companies can deploy customized, dedicated secure network hubs globally within a matter of minutes. Perimeter 81 truly shines in its granular access controls and highly detailed administrative activity auditing. This critical feature ensures strict, verifiable compliance with modern Indian data retention and privacy regulations. The cloud platform natively supports advanced split tunneling and automatic public Wi-Fi security protocols. It seamlessly protects remote workers the precise second they connect to an untrusted local network. Identity verification requires strict multi-factor authentication, ensuring only authorized personnel enter the digital perimeter.
| Technical Details | Perimeter 81 Specification |
|---|---|
| **Architecture Type** | Cloud-native Software Defined Perimeter (SDP) |
| **Compliance Level** | SOC 2 Type 2, strict GDPR, and HIPAA |
| **Primary Structural Benefit** | Instant, hardware-free cloud network deployment |
| **Ideal Corporate Fit** | High-compliance financial and technological firms |
Frequently Asked Questions
01 What is a VPN and why do remote workers in India need it?
A VPN creates a secure, mathematically encrypted connection over the notoriously vulnerable public internet. Indian remote workers absolutely need it to protect highly sensitive corporate data from malicious interception.
02 How does a VPN protect corporate data on public Wi-Fi in cafes?
It forcefully routes your internet data through a heavily encrypted, completely private digital tunnel. Hackers lurking on the exact same cafe network simply cannot read your intercepted, scrambled information.
03 Does using a VPN slow down my internet connection during peak hours?
Premium corporate VPNs actively minimize speed loss by utilizing advanced, lightweight protocols like WireGuard. Split tunneling further prevents slowdowns by smartly routing non-essential internet traffic through local, unencrypted connections.
04 Are VPNs legal for professional use in India under current IT rules?
Yes, using a secure VPN is entirely, one hundred percent legal within India today. Corporate VPNs are actually legally mandated by many IT departments for strict client data compliance.
05 What is the difference between a free VPN and a corporate-grade VPN?
Free VPNs notoriously sell user data and constantly provide slow, highly unstable internet connections. Corporate-grade VPNs offer legally binding no-log policies, dedicated high speeds, and strict, granular access controls.
06 How does split tunneling help maintain low latency for Indian users?
Split tunneling technically separates your heavy corporate traffic from your general, everyday internet browsing. This smart separation drastically reduces central server load, lowering latency for critical, real-time business applications.

WebHostRadar
Author
Expert in web hosting, VPNs, and online infrastructure.




